As you can see, CAPTCHA is becoming a bigger problem for users than for computers. You must be wondering—can we do it better?
Alternatives to CAPTCHA
There are numerous alternatives to CAPTCHA, just few of which I’ll talk about:
- Logging in via already-created account—for instance, Facebook, Twitter, and LinkedIn offer recognizable identities as a service
Advantages: easy to use and to implement
Disadvantages: possible privacy concerns of users
- Blocking registrations from suspicious IP addresses on the server side using services such as the BlackList DataBase—services have blacklists of IP addresses that are created automatically by spam activity or manually by reporting from users
Advantages: a robust solution
Disadvantages: slower than client-side validation and is vulnerable to errors, as blacklists may contain incomplete or incorrect information
- Honeypot method—the principle of this method consists of a fake field visible only to bots, hidden from users by CSS, and if the field is empty upon form submission, it’s likely a user; otherwise, it’s a bot
Advantages: an easy-to-implement solution
Disadvantages: users with password managers might have problems with Autofill, or problems can arise if a user has disabled CSS
- Tracking time from page load until form submission—real users need some time to scroll down a page and submit a form, while bots fill forms instantly
Advantages: easy to implement and can be a really good complementary solution
Disadvantages: users with password managers might have problems with Autofill
Solution on Kentico.com
CAPTCHA on Kentico.com was implemented for the aforementioned reason: to reduce and prevent spam attacks. It seems to work just fine, but we have started to observe that some users have problems with displaying CAPTCHAs. These problems occurred mostly on mobile devices or with low-speed internet connections, which made us think about whether or not we still want to bother users with CAPTCHA.
On the other hand, it’s really hard to secure your website only with these alternative approaches since they are mostly focused on client-side validation, and that can be bypassed (e.g., JavaScript can be disabled, Cookies can be changed, etc.).
For the implementation, we chose a combination of the Honeypot method, CAPTCHA (we are using the form control new reCAPTCHA), and server-side validation. CAPTCHAs are hidden and not required by default, and we have a fake address field as a honeypot. If the fake address is empty upon form submission, we can assume it’s a real user, so we allow them to submit the form without needing to solve a CAPTCHA. If the fake address field is not empty, a CAPTCHA is displayed and the user has to solve it.
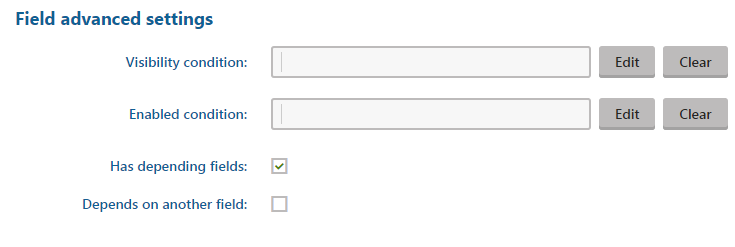
How to set up a fake address field
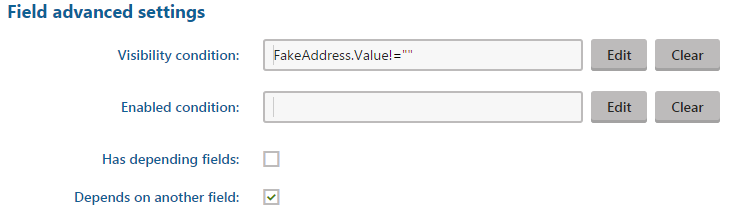
How to set up the CAPTCHA field
How to implement the server-side validation
A smart bot can bypass this client-side validation if it doesn’t fill the fake address field, which is why we also have a server-side check for repeating form submissions (we work with the assumption that a bot tries to submit forms repeatedly). If the previous submission was from the same user, we won’t count the submission and instead show an error message.
/// <summary>
/// OnBeforeSave event handler
/// </summary>
void viewBiz_OnBeforeSave(object sender, EventArgs e)
{
BizFormInfo formInfo;
DataClassInfo formClass;
string formName = viewBiz.FormName;
string registrationEmail = viewBiz.GetFieldValue("Email") as string;
formInfo = BizFormInfoProvider.GetBizFormInfo(formName, KenticoHelper.KENTICOCOM_SITENAME);
var lastItem = GetLastSubmittedFormItem(formInfo);
// Check if last inserted item was submitted by same user (by email)
if ((lastItem != null) && (lastItem.GetStringValue("Email", String.Empty).Equals(registrationEmail, StringComparison.OrdinalIgnoreCase)))
{
// If any new value was specified update original item and send notification email with data from form
if (UpdateOriginalItemWithFormValues(lastItem, viewBiz) && viewBiz.EnableNotificationEmail)
{
viewBiz.SendNotificationEmail(registrationEmail, formInfo.FormSendToEmail, lastItem, formInfo);
}
// Don't save current item just redirect to 'thank you' page
viewBiz.StopProcessing = true;
string redirectToUrl = ContextResolver.ResolveMacros(formInfo.FormRedirectToUrl);
Response.Redirect(URLHelper.ResolveUrl(redirectToUrl));
}
}
/// <summary>
/// Returns last submitted form item
/// </summary>
private BizFormItem GetLastSubmittedFormItem(BizFormInfo formInfo)
{
var formClass = DataClassInfoProvider.GetDataClassInfo(formInfo.FormClassID);
var lastItemQuery = BizFormItemProvider.GetItems(formClass.ClassName).
TopN(1).
OrderByDescending("FormInserted");
return lastItemQuery.FirstOrDefault();
}
Conclusion
CAPTCHA is a good tool for protecting yourself from spambots, but you have to use it wisely so it doesn’t discourage your users from converting. As you can see from our real example, you can combine a few easy-to-implement solutions, and they can serve you just as well. What is your opinion on CAPTCHA? Do you have any interesting alternatives you want to share with us? Don’t hesitate to leave us a comment.