Security improvements in Kentico CMS 7
We at Kentico take the security of our product very seriously. That’s why we implement security improvements into every new version. Kentico CMS 7 is not an exception, so let‘s take a look at what’s new.
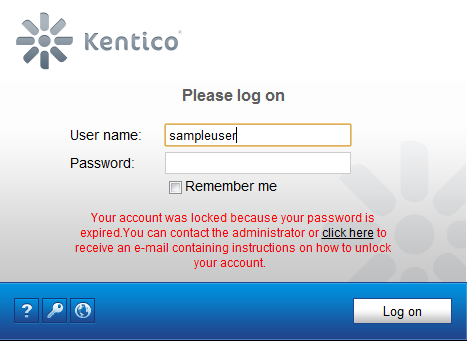
Password expiration
There is a new option to set up password expiration time for a user. After the given period, the user will see a warning, or her account will be locked (disabled) until she changes the password. The picture below shows the second case (account lock). All configuration settings can be found in Site Manager -> Settings -> Security & Membership -> Passwords, in the Password expiration group.
You can extend the user’s password validity in CMS Desk/Site Manager -> Administration -> Users -> Edit a user. There, you will see whether the password expired or when it is going to expire. You can click the Extend validity button, which extends the validity to the maximum value. You can adjust that using the Password expiration period setting.
The “Expired password” warning message is visible always in CMS Desk and Site Manager. There is also a new web part called Password expiration, which shows a warning with an expired password message.
There is also an option to show the user a warning message a specified number of days before the password expires. This warning is shown in CMS Desk and Site Manager as well.
Finally, you can influence whether the logon screen shows the reason of an account lock in the message or not by the setting key Display account lock information message. You can find this setting in Settings -> Security & Membership -> Protection, in the General group.
Invalid logon attempts
This feature has some behavior shared with the previous one. When a user enters a wrong password N times, her account will be locked. Then, the user receives an e-mail with instructions how to unlock it. The logon screen shows the message with information about account lock because of invalid logon attempts (only if the Display account lock information message setting key is turned on).
All settings related to this feature are placed in Settings -> Security & Membership -> Protection, in the Invalid logon attempts group. Here you can enable/disable this feature, set up the maximum number of attempts and the path where the user is pointed to reset her password.
You can reset the number of invalid logon attempts for the user in CMS Desk/Site Manager -> Administration -> Users -> Edit a user. Here you can see the number of invalid attempts and you can reset it by clicking the Reset button.
Password policy enforcement
In Kentico CMS 6 we introduced the Password policy feature. Kentico CMS 7 will contain one handy enhancement. If a user has a password that doesn’t meet the password policy, she will be forced to change it the next time she logs in to the system. After the login, a similar screen is shown to the user if the policy is not met.
Screen lock
I believe that this functionality will help you from both security and usability points of view. When a user doesn’t send any request to a web site for the specified amount of time, their screen is locked. The screen lock works only in CMS Desk and Site Manager. After the screen gets locked, you will have to either enter the password to unlock it or sign out.
The user’s session is kept alive all the time so after the user enters the password, the screen is unlocked and she can continue working at the exact same place.
Before the screen gets locked, you will see a warning with the number of seconds after which your screen will be locked. There is also a link for cancelling, so you don’t need to refresh the page just because you want to prevent the screen from getting locked.
Both screen lock interval and warning interval are configurable in the Security & Membership -> Protection settings category, in the Screen lock group.
E-mail confirmation of a subscription
You probably know that in Kentico CMS 6, we implemented an e-mail confirmation for newsletter subscribers. In Kentico CMS 7, we extended the e-mail confirmations on Forums (forums, forum threads, and forum posts), Blogs (blog comments) and Message boards. The e-mail confirmation is configurable on global level and site level (settings in Site Manager) as well as on object level (in the editing UI of a particular object).
Session attacks protection
There are lots of attacks that abuse the victim’s session, for example the session fixation attack. In this kind of attack, hackers either get into the user’s session or slip them their own in order to share one session with them. To mitigate the risk, there is a new option to abandon the user’s session and renew the session ID after the user logs in or out.
This protection could have unpleasant consequences because the user loses her session data (for example the content of the current shopping cart) during the authentication process. Please bear in mind that you always have to find the right balance between security and functionality of your website.
Clickjacking protection
Clickjacking is a very popular attack in these days. A typical attack scenario is that an attacker adds a target website into a frame to her website. The attacker covers the frame with different content (a video with funny moments for example,) and sends a link to this website to the victim. The victim clicks on the area with the frame (to see the video) but clicks on the target site and performs an action without realizing that.
To prevent such attack, the best practice is to send the following HTTP header to the client:
X-Frame-Options SAMEORIGIN
This header says that a page could be rendered in a frame only in the same domain as the parent page. This header is supported by all modern web browsers. We add this header to all HTTP responses by default. You can exclude certain paths by specifying them in the application setting key CMSXFrameOptionsExcluded in the web.config (when you specify “/” you disable this protection completely).
Disabling Autocomplete for user name on login form
When you enter text into a search field on a website and press the search button, the data you entered is automatically remembered by the browser. The next time the browser will try to complete your text as you are writing it. This feature is called Autocomplete and it can be quite useful for operations like searching. But on login forms this behavior is not that useful. A computer could be shared by multiple users and all of them could see the user names of others. That’s why you have an easy way how to turn off Autocomplete on all standard login forms (logon page and all logon web parts). You can find this option in Settings -> Security & Membership -> Protection, in the General group. This setting key is named Enable Autocomplete.
And that’s all for today, I hope you’ll like these security enhancements. Tell us your opinion through the comments.